

Unlock your business potential
Find, convert, and keep more customers with LocaliQ’s growth marketing platform. We offer innovative technology and unparalleled expertise to move your business forward.

Unlock your business potential
Find, convert, and keep more customers with LocaliQ’s growth marketing platform. We offer innovative technology and unparalleled expertise to move your business forward.
Elevate your business with the power of LocaliQ
With 20+ years of experience, our proven record of innovation and performance in the digital marketing industry will help you drive results.
Take control of your business goals
with a team of experts behind you
Feel secure knowing you have a partner
that will help you get ahead

Tap into actionable data and insights
with our smart technology
Unlock your business potential
Find, convert, and keep more customers with LocaliQ’s growth marketing platform. We offer innovative technology and unparalleled expertise to move your business forward.


Elevate your business with the power of LocaliQ
Take control of your business goals
with a team of experts behind you
Feel secure knowing you have a partner
that will help you get ahead

Tap into actionable data and insights
with our smart technology
Dedicated to helping local businesses succeed
Products & Services
Built for you and your needs
Be more efficient in your marketing with our all-in-one growth platform. We’ll equip your business with the tools you need to succeed – and thrive.


Find leads and build
your online presence
What we can do for you:
-
Create captivating websites and landing pages
-
Manage and analyze your listings
-
Improve SEO, manage your social media accounts, create content, and more
Scale up your business
What we can do for you:
-
Optimize and manage your search ads
-
Create targeted display ads, video ads, social ads, email marketing, and custom promotions
-
Manage social ads, delivery, and reporting

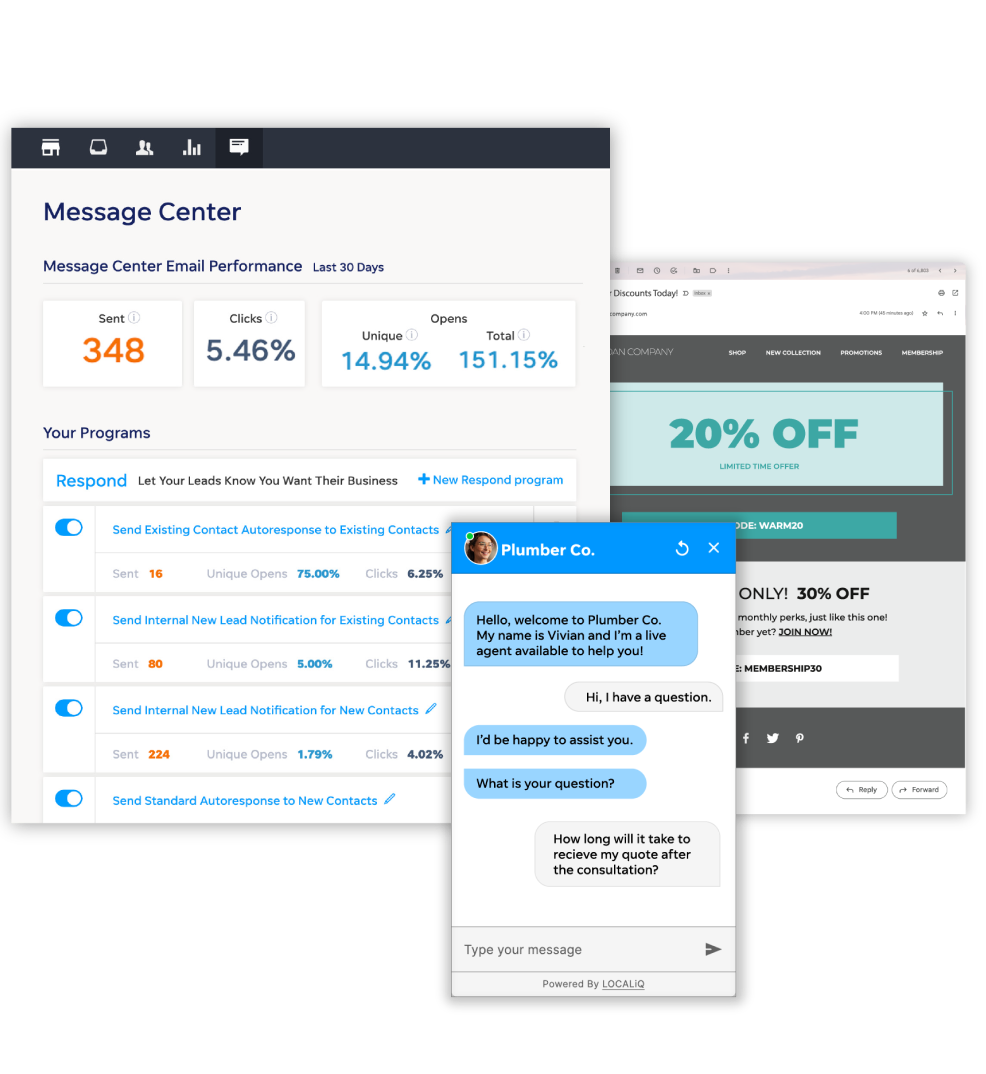
Convert and keep your customers
What we can do for you:
-
Manage your leads, automate marketing, and provide call tracking and recording
-
Monitor and manage live chat 24/7
-
Get instant transcripts, lead qualification, and reporting
Free Website Grader
How does your online presence stack up?
Our Website Grader does more than just evaluate your site performance – it reviews your social media presence and the effectiveness of your digital advertising. Best part? It only takes a few minutes.

Keep up with the latest from LocaliQ


We’ve got your back
Partner with LocaliQ and you can feel confident knowing we’ll help you every step of the way.
4.82
out of 5 on our customers satisfaction score
![]()
3x winner
Google Quality Account Champion award in North America
4 out of 5
customers would strongly recommend LocaliQ

Trusted by 440K+ businesses
Get the power of LocaliQ behind you
Let us help you seize your potential.









